Announcing the World's Strongest Security Myriad Key Multiple Time-Variant Formation Point Theory "Awesomeness Edition No need to remember or input PINs or IDs
~Multiple Key Multiple Time-Variant Establishment Point Theory ~ "Awesomeness Edition"
株式会社ポイント機構
The Point Organization, Inc. (Head office: Shibuya-ku, Tokyo; Representative Director: Yuki Takeuchi; hereafter, "Point Organization"), which operates the point redemption system "A-GEL Gift Point," has applied for a patent for a new theory called "Myriad Key Multiple Time-Variant Formation Point Theory," which reviews the structure itself, together with K-Trust Corporation (Head office: Moriyama-ku, Nagoya City, Aichi Prefecture; Representative Directors: Tomoko Hirakawa and Kazunori Hirakawa; hereafter, "K-Trust"). (headquartered in Moriyama-ku, Nagoya, Aichi; Tomoko Hirakawa and Kazunori Hirakawa, CEOs; hereinafter "K Trust") have applied for a patent for a new theory, the "infinite-key multiple time-varying fixed point theory," which reviews this structure itself. Some parts of this theory have already been patented. We will explain the weaknesses of conventional methods of security and the difference in reverse proof between conventional methods and the new design concept.
Cyber-attacks against companies and local governments are becoming more sophisticated and sophisticated every year. Behind this is the structure of repeated trial and learn attacks.
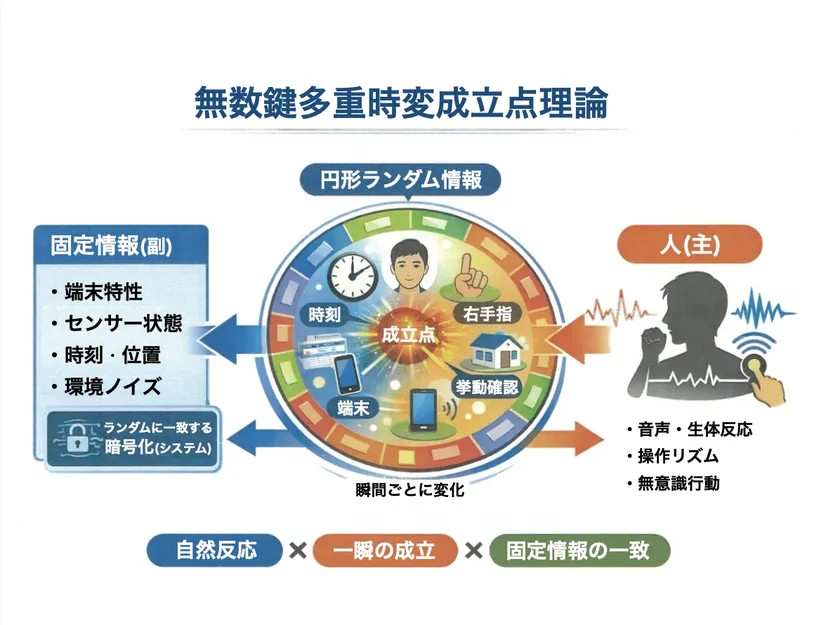
Theory of Multiple Time-Variant Formation Points with Infinite Number of Keys
The design is such that the answer to the question is determined only when the user logs in to the system.
The first video you will see is
https://youtu.be/IkQZSjOUpOQ?si=EqWjExx3hztd6iCJ
The video of the amazing theory of infinite-key multiple time-varying fixed-points.
https://youtu.be/7k7DGSXJbiw?si=dpXxBCTYFI6dltap
▼Explanatory video of some of the patented multiple composite patent rights
https://youtu.be/hxV3rdUfklY?si=cvV4BIYRDmiFwaAT
Problems with conventional security
Many security,
IDs
Passwords
PINs
Many security systems are based on "fixed correct answers" that people memorize and enter. However, there are major problems with this method.
Problem (1): Once leaked, it can be used any number of times.
Problem (2): Attackers can try as many times as they want.
Problem (3): AI can learn how to attack.
In other words, the structure of the attack is "the more times the attacker tries, the better".
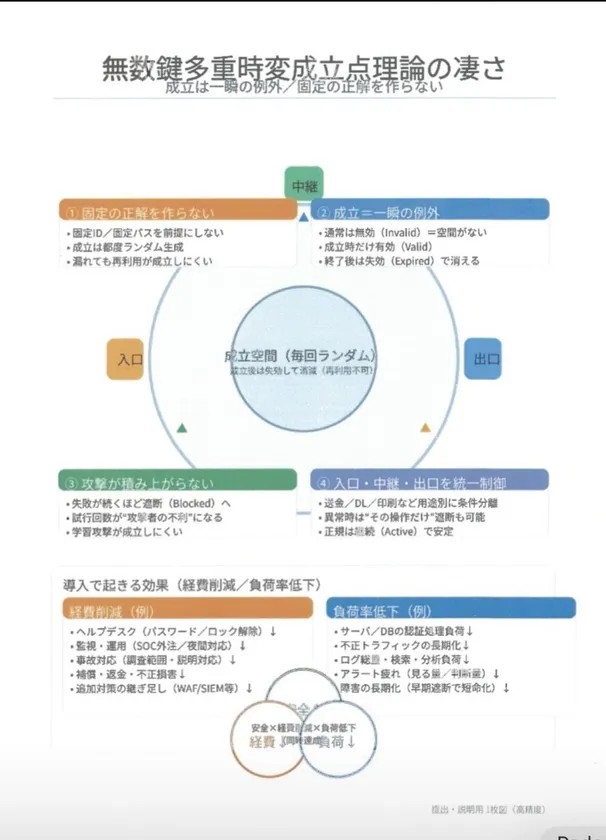
Major differences of this theory
In the infinite-key multiple-time-variable point theory, "fixed correct answers (PINs or IDs)" are not used. Instead, it uses the following structure.
Feature (1) No need to remember PINs or IDs
Conventionally
Input ID
Input password
OTP input
etc., which required a person to remember and input the PIN.
In this theory,
Natural human response
Terminal status
Time of day
Time ● Environmental information
The theory automatically determines the conditions for the PIN by combining the following factors: ● Natural human reaction ● Terminal status In other words, there is no need for a person to remember his/her PIN.
Feature (2) Multiple logins exist in a single login.
A normal login is "one login = one session. However, in this theory, in a login
Entrance
Relay
Exit
Each of them has a different condition for establishment. For example
Login is established
Browsing successful
Transfer approved
Download successful
For example, a single login can have multiple success points, such as ● Login success ● Browsing success ● Remittance success ● Download success
Feature (3) Multiple encryption keys are used in the lottery
Conventional
One password
One key
This theory
Multiple keys
Random each time
● Changes every hour
In other words, it is a "lottery structure" where the key changes every time. Therefore
Guess
Bingo
Reuse
Reuse is difficult to achieve.
Feature (4) Attacks do not pile up
Conventional
Attacker
→ Failed
→ Try again
→ Try again
→ Keep trying until success
this theory
Aggressor
→ Fail
→ Intercept
→ Strengthen conditions
→ Space annihilation
In other words, the longer the attacker continues to attack, the more disadvantageous the structure becomes.
Summary of the characteristics of this theory
Comparison with 73 types of attacks
In this video,
Phishing
AI voice spoofing
Deep Fakes
Password brute force
Session hijacking
API key compromise
Ransomware
Ransomware ● Internal fraud
Server intrusion
AI attacks
The comparison is based on 73 different attack models, including As a result, many attacks are blocked before they can be established.
Effects in Figures (Design Model)
In the theoretical model,
Prevention rate: 99% or more
Damage probability: 0.3% or less
Improvement factor: hundreds of millions to hundreds of billions of times
The theoretical model shows the following design indexes. However, these are theoretical model values, not empirical values.

Design Model
The most important point of this theory
Ordinary security is a structure that "protects the correct answer. This theory, however, is a structure that "allows for the establishment of a momentary exception. In other words, the object to be protected is not the secret, but the "state of being valid.
In a word
The theory of infinite-key multiple time-varying fixed points is a theory that changes the concept of security from security that protects a fixed correct answer to security that only allows a momentary exception to be made.
Future video release schedule
Following the "Greatness" section of this issue, we will be releasing the following videos,
Introduction (Basic Concepts)
Basic (Theoretical Structure)
Comprehensive version (social implementation and national application)
The "Greatness" section will be followed by ● Introductory section (Basic concepts) ● Basic section (Theoretical structure)
About Point Organization, Inc.

The Point Organization, Inc.
Company name: The Point Organization, Inc.
Representative: Yuki Takeuchi, Representative Director
Head office: Room 301, HOUSE 2717, 2-7-9 Sendagaya, Shibuya-ku, Tokyo
Date of establishment: December 24, 2021
Fiscal year end: March
URL : https://point-kikou.co.jp/
Official website of the FSA Supervisory Public Search (Edinet) URL:
https://disclosure2.edinet-fsa.go.jp/WEEE0030.aspx?bXVsPeODneOCpOODs+ODiOapn+aniyZjdGY9b24mZmxzPW9uJmxwcj1vbiZycHI9b24mb3RoPW9 uJnBmcz03Jnllcj0mbW9uPQ==
About K Trust Co.

K Trust Co.
Company name: K Trust Co.
Representative: Tomoko Hirakawa and Kazunori Hirakawa, Representative Directors
Headquarters : 1-3313 Shimoshidami, Moriyama-ku, Nagoya, Aichi, Japan
URL : https://www.ktrust.info
Relationship with Point Organization: Sole agent for A-GEL gift points & A-GEL gift cards
- Category:
- Corporate Trends
- Genres:
- Technology General Business Economy(Japan)